Understanding and Mitigating Common Input Security Risks
Learn about SQL Injection, Cross Site Scripting, Denial of Service, and more. Explore mitigation techniques to secure your applications.

Understanding and Mitigating Common Input Security Risks
E N D
Presentation Transcript
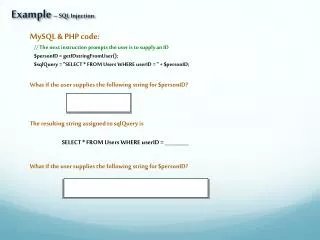
Example – SQL Injection MySQL & PHP code: // The next instruction prompts the user is to supply an ID $personID = getIDstringFromUser(); $sqlQuery = "SELECT * FROM Users WHERE userID = " + $personID; What if the user supplies the following string for $personID? The resulting string assigned to sqlQuery is SELECT * FROM Users WHERE userID = _________ What if the user supplies the following string for $personID?
Input Validation – common associated risks • ______________ • user input controls SQL statements ultimately executed • by a database server • http://www.tizag.com/mysqlTutorial/mysql-php-sql-injection.php • ______________ • user input controls file access location – the “double-dot attack” • ______________ • user input controls file naming in such a way as to get a program to • read, write or delete files that should be protected • Denial of Service • user input controls causes application to consume excessive resources • or simply stop executing due to unacceptable input • _______________ • user input controls causes the application to reveal confidential information • perhaps this information can be used as part of a more sophisticated attack Please check out OWASP
more common associated risks • Cross Site Scripting (XSS) • user input controls injects HTML or script commands into Web • application causing the Web application to breach its security • http://www.acunetix.com/websitesecurity/xss.htm <html> <head> <title>My Javascript Page</title> </head> <body> type your name here >>> <input type="text" id="userInput"></input> <button onclick="buttonHandler()">Submit</button> <script> var thing = "blah"; function buttonHandler() { var stuff = document.getElementById("userInput").value; document.write(stuff); } </script> </body> </html>
still more common associated risks • ______________ • user input injects commands, often via meta-characters, that cause • a server to perform unintended functions • Buffer Overflows • user input controls exceeds limits in a way that allows the attacker • to control application behavior
Before Mitigation Step 1 - user interface files parameters of externally-invoked methods network sockets/ports network certificates URLs (passed to Web servers) cookies Step 2 - Step 3 –
Mitigation Techniques Bounds Checking Pattern Matching Data Reflecting Sanitizing Double Decoding Escaping Text Full Syntactic Analysis Exception Handling
Escaping Text Escaping individual characters is a particularly effective way of mitigating XSS.