Last class
Last class. Ethernet Hubs and Switches Mobile and wireless networks, CDMA Today CDMA and IEEE 802.11 wireless LANs Network security. twisted pair. hub. 10BaseT and 100BaseT Ethernet. Uses CSMA/CD 10/100 Mbps rate; latter called “fast ethernet” T stands for Twisted Pair

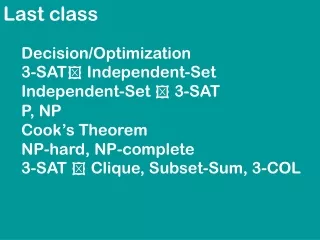
Last class
E N D
Presentation Transcript
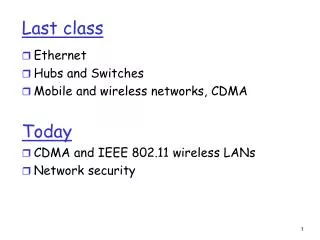
Last class • Ethernet • Hubs and Switches • Mobile and wireless networks, CDMA Today • CDMA and IEEE 802.11 wireless LANs • Network security
twisted pair hub 10BaseT and 100BaseT Ethernet • Uses CSMA/CD • 10/100 Mbps rate; latter called “fast ethernet” • T stands for Twisted Pair • Nodes connect to a hub: “star topology”; 100 m max distance between nodes and hub
Interconnecting with hubs Pros: • Enables interdepartmental communication • Extends max distance btw. nodes • If a hub malfunctions, the backbone hub can disconnect it Cons: • Collision domains are transferred into one large, common domain • Cannot interconnect 10BaseT and 100BaseT hubs hub hub hub hub
switch hub hub hub Switch: traffic isolation • switch installation breaks subnet into LAN segments • switch filters packets: • same-LAN-segment frames not usually forwarded onto other LAN segments • segments become separate collision domains collision domain collision domain collision domain
B A C C C’s signal strength A’s signal strength B A space Wireless network characteristics Multiple wireless senders and receivers create additional problems (beyond multiple access): Hidden terminal problem • B, A hear each other • B, C hear each other • A, C can not hear each other means A, C unaware of their interference at B Signal fading: • B, A hear each other • B, C hear each other • A, C can not hear each other interferring at B
Overview • CDMA and IEEE 802.11 wireless LANs • Network security
Code Division Multiple Access (CDMA) • used in several wireless broadcast channels (cellular, satellite, etc) standards • unique “code” assigned to each user; i.e., code set partitioning • all users share same frequency, but each user has own “chipping” sequence (i.e., code) to encode data • encoded signal = (original data) X (chipping sequence) • decoding: inner-product of encoded signal and chipping sequence • allows multiple users to “coexist” and transmit simultaneously with minimal interference (if codes are “orthogonal”)
d0 = 1 1 1 1 1 1 1 d1 = -1 1 1 1 1 1 1 1 1 1 1 1 1 1 1 1 1 1 1 1 1 1 1 1 1 1 1 - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - 1 1 1 1 1 1 1 1 1 1 1 1 1 1 1 1 1 1 1 1 1 1 1 1 1 1 1 1 1 1 1 1 M Di = SZi,m.cm m=1 M d0 = 1 d1 = -1 CDMA Encode/Decode channel output Zi,m Zi,m= di.cm data bits sender slot 0 channel output slot 1 channel output code slot 1 slot 0 received input slot 0 channel output slot 1 channel output code receiver slot 1 slot 0
Overview • CDMA and IEEE 802.11 wireless LANs • Network security
802.11b 2.4-5 GHz unlicensed radio spectrum up to 11 Mbps direct sequence spread spectrum (DSSS) in physical layer all hosts use same chipping code widely deployed, using base stations 802.11a 5-6 GHz range up to 54 Mbps 802.11g 2.4-5 GHz range up to 54 Mbps All use CSMA/CA for multiple access All have base-station and ad-hoc network versions IEEE 802.11 Wireless LAN
AP AP Internet 802.11 LAN architecture • wireless host communicates with base station • base station = access point (AP) • Basic Service Set (BSS) (aka “cell”) in infrastructure mode contains: • wireless hosts • access point (AP): base station • ad hoc mode: hosts only hub, switch or router BSS 1 BSS 2
802.11: Channels, association • 802.11b: 2.4GHz-2.485GHz spectrum divided into 11 channels at different frequencies • AP admin chooses frequency for AP • interference possible: channel can be same as that chosen by neighboring AP! • host: must associate with an AP • scans channels, listening for beacon frames containing AP’s name (SSID) and MAC address • selects AP to associate with • may perform authentication [Chapter 8] • will typically run DHCP to get IP address in AP’s subnet
B A C C C’s signal strength A’s signal strength B A space IEEE 802.11: multiple access • avoid collisions: 2+ nodes transmitting at same time • 802.11: CSMA - sense before transmitting • don’t collide with ongoing transmission by other node • 802.11: no collision detection! • difficult to receive (sense collisions) when transmitting due to weak received signals (fading) • can’t sense all collisions in any case: hidden terminal, fading • goal: avoid collisions: CSMA/C(ollision)A(voidance)
DIFS data SIFS ACK IEEE 802.11 MAC Protocol: CSMA/CA 802.11 sender 1 if sense channel idle for DIFSthen transmit entire frame (no CD) 2 ifsense channel busy then - start random backoff time - timer counts down while channel idle - transmit when timer expires - if no ACK, increase random backoff interval, repeat 2 802.11 receiver - if frame received OK return ACK after SIFS (ACK needed due to hidden terminal problem) sender receiver
Avoiding collisions (more) idea: allow sender to “reserve” channel rather than random access of data frames: avoid collisions of long data frames • sender first transmits small request-to-send (RTS) packets to BS using CSMA • RTSs may still collide with each other (but they’re short) • BS broadcasts clear-to-send CTS in response to RTS • RTS heard by all nodes • sender transmits data frame • other stations defer transmissions Avoid data frame collisions completely using small reservation packets!
RTS(B) RTS(A) reservation collision RTS(A) CTS(A) CTS(A) DATA (A) ACK(A) ACK(A) Collision Avoidance: RTS-CTS exchange B A AP defer time
6 4 2 2 6 6 6 2 0 - 2312 frame control duration address 1 address 2 address 3 address 4 payload CRC seq control 802.11 frame: addressing Address 4: used only in ad hoc mode Address 1: MAC address of wireless host or AP to receive this frame Address 3: MAC address of router interface to which AP is attached Address 2: MAC address of wireless host or AP transmitting this frame
router AP Internet R1 MAC addr AP MAC addr source address dest. address 802.3frame AP MAC addr H1 MAC addr R1 MAC addr address 3 address 2 address 1 802.11 frame 802.11 frame: addressing H1 R1
H1 remains in same IP subnet: IP address can remain same switch: which AP is associated with H1? self-learning (Ch. 5): switch will see frame from H1 and “remember” which switch port can be used to reach H1 router 802.11: mobility within same subnet hub or switch BBS 1 AP 1 AP 2 H1 BBS 2
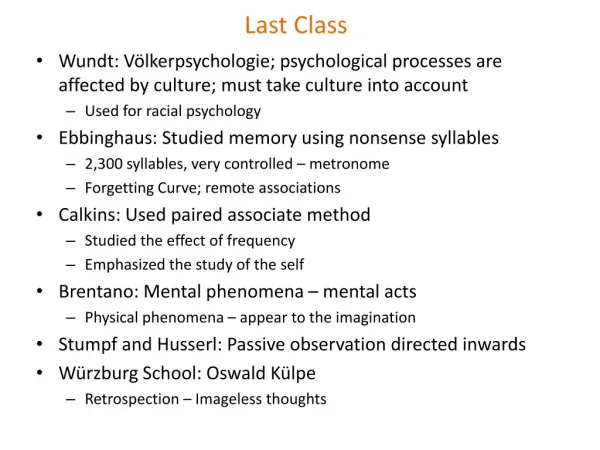
Network Security What is network security? Principles of cryptography Authentication Access control: firewalls Attacks and counter measures
What is network security? Confidentiality: only sender, intended receiver should “understand” message contents • sender encrypts message • receiver decrypts message Authentication: sender, receiver want to confirm identity of each other Message Integrity: sender, receiver want to ensure message content not altered (in transit, or afterwards) without detection Access and Availability: services must be accessible and available to users
Friends and enemies: Alice, Bob, Trudy • well-known in network security world • Bob, Alice (lovers!) want to communicate “securely” • Trudy (intruder) may intercept, delete, add messages Alice Bob data, control messages channel secure sender secure receiver data data Trudy
Who might Bob, Alice be? • … well, real-life Bobs and Alices! • Web browser/server for electronic transactions (e.g., on-line purchases) • on-line banking client/server • DNS servers • routers exchanging routing table updates • other examples?
There are bad guys (and girls) out there! Q: What can a “bad guy” do? A: a lot! • eavesdrop: intercept messages • actively insert messages into connection • impersonation: can fake (spoof) source address in packet (or any field in packet) • hijacking: “take over” ongoing connection by removing sender or receiver, inserting himself in place • denial of service: prevent service from being used by others (e.g., by overloading resources) more on this later ……
Overview What is network security? Principles of cryptography Authentication Access control: firewalls Attacks and counter measures
K K A B The language of cryptography Alice’s encryption key Bob’s decryption key symmetric key crypto: sender, receiver keys identical public-key crypto: encryption key public, decryption key secret (private) encryption algorithm decryption algorithm ciphertext plaintext plaintext
Symmetric key cryptography substitution cipher: substituting one thing for another • monoalphabetic cipher: substitute one letter for another plaintext: abcdefghijklmnopqrstuvwxyz ciphertext: mnbvcxzasdfghjklpoiuytrewq E.g.: Plaintext: bob. i love you. alice ciphertext: nkn. s gktc wky. mgsbc • Q: How hard to break this simple cipher?: • brute force (how hard?) • other?
K K A-B A-B K (m) m = K ( ) A-B A-B Symmetric key cryptography symmetric key crypto: Bob and Alice share know same (symmetric) key: K • e.g., key is knowing substitution pattern in mono alphabetic substitution cipher • Q: how do Bob and Alice agree on key value? encryption algorithm decryption algorithm ciphertext plaintext plaintext message, m K (m) A-B A-B
Symmetric key crypto: DES DES: Data Encryption Standard • US encryption standard [NIST 1993] • 56-bit symmetric key, 64-bit plaintext input • How secure is DES? • DES Challenge: 56-bit-key-encrypted phrase (“Strong cryptography makes the world a safer place”) decrypted (brute force) in 4 months • no known “backdoor” decryption approach • making DES more secure: • use three keys sequentially (3-DES) on each datum • use cipher-block chaining
DES operation Symmetric key crypto: DES initial permutation 16 identical “rounds” of function application, each using different 48 bits of key final permutation
AES: Advanced Encryption Standard • new (Nov. 2001) symmetric-key NIST standard, replacing DES • processes data in 128 bit blocks • 128, 192, or 256 bit keys • brute force decryption (try each key) taking 1 sec on DES, takes 149 trillion years for AES
Public Key Cryptography symmetric key crypto • requires sender, receiver know shared secret key • Q: how to agree on key in first place (particularly if never “met”)? public key cryptography • radically different approach [Diffie-Hellman76, RSA78] • sender, receiver do not share secret key • public encryption key known to all • private decryption key known only to receiver
+ K (m) B - + m = K (K (m)) B B Public key cryptography + Bob’s public key K B - Bob’s private key K B encryption algorithm decryption algorithm plaintext message plaintext message, m ciphertext
K (K (m)) = m B B - + 1 2 Public key encryption algorithms Requirements: need K ( ) and K ( ) such that . . + - B B + given public key K , it should be impossible to compute private key K B - B RSA: Rivest, Shamir, Adelson algorithm