The Final Present
The Final Present . Lee Jeng-Shiou Computer Network of E.E. Outline. Throughput Analysis Review for Single-hop Networks Throughout Analysis for Multi-hop Networks Mathematical Analysis of the String Topology Analytical and Simulation Results


The Final Present
E N D
Presentation Transcript
The Final Present Lee Jeng-Shiou Computer Network of E.E
Outline • Throughput Analysis Review for Single-hop Networks • Throughout Analysis for Multi-hop Networks • Mathematical Analysis of the String Topology • Analytical and Simulation Results • An Alternative Mathematical Analysis of the String Topology • Conclusion
Throughput Analysis Review for Single-hop Networks • (s(t), b(t)) • s(t): the backoff stage • b(t): the backoff time counter • p: the conditional collision probability • τ: the probability that a station transmits in a generic slot time
Throughput Review for Single-hop Networks (cont~) • The transmission probability τ in a randomly chosen ”generic” slot is • The collision probability is expressed by • Throughput S is obtained by
Throughout Analysis for Multi-hop Networks • We concentrate on the impact of the hidden node problem. • We analyze the throughput based on a single station’s point of view. • The analysis method is similar to the single-hop case. • Obtaining the stationary probability τ using a Markov model. • Expressing the throughput as function of τ by studying the events that can occur within a generic slot time.
Throughout Analysis for Multi-hop Networks • Assumption: • All packets are destined for neighbor nodes. • There is no capture effect. • Each station always has packets to transmit.
A1 R=r A B A Simplified Condition • The carrier sense range is equal to the transmission range.
A Simplified Condition (cont~) • The simulations have been done by the network simulator - ns2. • Simulation area 1500x1500 m2. • We consider five topology scenarios and each scenario includes four traffic patterns. • Each node generates packets based on CBR model with packet sizes 256, 512, 1024 and 2048 bytes. • They correspond to packet arrival interval of 0.0013, 0.0026, 0.0052 and 0.01 sec.
A1 R r A B A Realistic Carrier Sense Range • The carrier sense range is 550 meters and the transmission range is 250 meters.
Conclusions • The throughput performance of the IEEE 802.11 DCF scheme in multi-hop ad hoc networks is analyzed. • It also shows the proposed model is accurate when degenerated into single-hop networks. • The throughput of a single station is decreased as the number of stations increases. • The total throughout almost stays at a constant value.
Conclusions (cont~) • The total network throughput is decreased as much as by 55% when the carrier sense range is equal to 550 meters. • The larger packet size results in the higher network throughput. • For spatial reuse factor, the results shows that there no clear relationship with the number of stations and packet size.
Mathematical Analysis of the String Topology (cont.) • Six possible situations observed by station 0 at the beginning of a slot.
Node 0 “idle” (1-τ) (cont.) • One of n1 and n2 Tx (P2) (assume n1 Tx)
success: n2 idle during • collision: n2 Tx during Tv
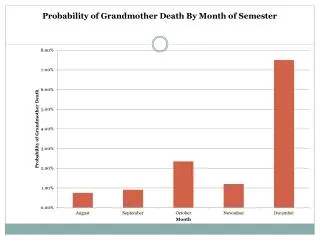
Analytical and Simulation Results (cont.) • The simulation throughput (13 stations) and the analytical throughput.
An Alternative Mathematical Analysis of the String Topology • One directional traffic between two stations • No collisions ->
An Alternative Mathematical Analysis of the String Topology (cont.) • The normalized throughput of the basic access scheme when there is one traffic.
An Alternative Mathematical Analysis of the String Topology (cont.) • The normalized throughput of the RTS/CTS access scheme when there is one traffic.
An Alternative Mathematical Analysis of the String Topology (cont.) • Bi-directional traffic between two stations • Collisions may occur. • Evaluating the average backoff time • All newly generated backoff values, such as X ,Y ,and M ,are identically distributed from uniform distribution. where A represents the CWmin
An Alternative Mathematical Analysis of the String Topology (cont.) • Let Z=|X-Y|. We have • A newly generated backoff value is M with the probability distribution as X, and Y. Let W=|M-Z|. We have • -> Z and W are identical distribution. • The expected backoff interval is
An Alternative Mathematical Analysis of the String Topology (cont.) • Evaluating the collision probability
An Alternative Mathematical Analysis of the String Topology (cont.) • The normalized throughput of the basic access scheme considering the collisions when there is two traffic.
An Alternative Mathematical Analysis of the String Topology (cont.) • The normalized throughput of the RTS/CTS access scheme considering the collisions when there is two traffic.
Conclusions • We first analyze the transmission behavior of stations in a string topology in the multi-hop environment. • In the presence of the hidden and exposed terminal problems, the mathematical analysis is more complicated compared to the single-hop wireless network. • From the analytical and simulation results, we find that a larger packet size can increase the normalized throughput.
Conclusions (cont.) • For future research, we will proceed with the alternative mathematical analysis. • We may discuss the behavior under the assumption that the carrier sensing range is much larger than the transmission range, and the capture effect may be included. • Besides, we may extend our one-dimension topology to different types of topology.
Conclusion • What we have done • We propose a new method to improve IEEE 802.11 performance and establish a model for analysis. • Simulation and comparison • What we are going to do • A general equation (even solution) for our model • More simulation