Computer Systems and Viruses: Basics Explained
Understand the components of a computer system, softcopy data, output information, viruses, alternative input methods like speech recognition, and key software functions. Learn about hardware, software, scanners, antivirus programs, and biometric devices in this comprehensive guide.

Computer Systems and Viruses: Basics Explained
E N D
Presentation Transcript
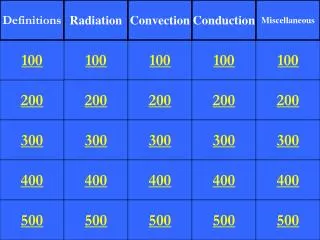
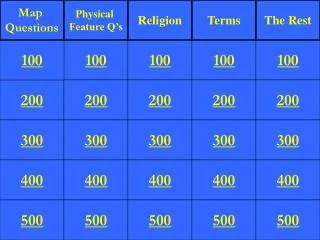
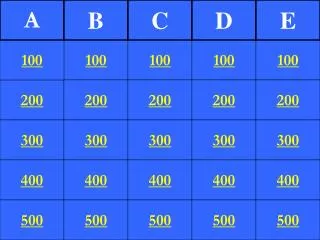
Computer Basics Systems Viruses Alternative Input Speech Recognition 100 100 100 100 100 200 200 200 200 200 300 300 300 300 300 400 400 400 400 400 500 500 500 500 500
Software packages used to create financial statements using mathematical calculations are:
What equipment is used like a copy machine to allow information to be input into the computer?
The operating system capability that permits more than one program to run simultaneously is called:
To protect the computer from detecting a virus the user should install a/an:
Which is a destructive computer code or virus that is designed to activate at a specific time?
Which is NOT a virus known to destroy or cause damage to computer files?
Which software allows the user to pay a small fee after the trial period?
The software that transforms spoken words into typed text is called:
What equipment allows the user to capture pictures and move them to the computer?
The input device that transfers images or text into a word processing document or e-mail is a:
What device or system measures a human characteristic for the purpose of identification?
A way of speaking that is characteristic of a geographic region is called a(n):
Which is necessary for speech recognition on a computer system?
What is the fastest number of words per minute that modern speech recognition systems can recognize speech?
A special file that collects data about a user’s speech patterns is called a:
The process in which a user reads a sample script aloud, enabling the speech recognition system to record an individual’s unique speech patterns is: