MAC Research Highlight
This research outlines significant issues in the analysis of the IEEE 802.11 Distributed Coordination Function (DCF) and proposes methods for performance enhancement. Key areas include performance under saturation, unfair access among multiple wireless links, and techniques for collision avoidance. The study references critical works, such as Bianchi's analysis of DCF performance and Kanodia's packet scheduling solutions in wireless ad hoc networks. It also discusses innovative protocols, including CARMA-NTG for efficient medium access control, focusing on reducing handoff latency and ensuring equitable channel usage.

MAC Research Highlight
E N D
Presentation Transcript
MAC Research Highlight Y.C. Tseng
Outline: 3 Main Research Issues • Analysis: • G. Bianchi, “Performance Analysis of the IEEE 802.11 Distributed Coordination Function”, IEEE J-SAC, 2000. • K. Kanodia et al., “Ordered Packet Scheduling in Wireless Ad Hoc Networks: Mechanisms and Performance Analysis”, ACM MobileHoc 2002. • Protocols: • R. Garces and J. J. Garcia-Luna-Aceves, "Collision Avoidance and Resolution Multiple Access with Transmission Groups", INFOCOM 2007. • B. P. Crow, J. G. Kim, & P. Sakai, "Investigation of the IEEE 802.11 Medium Access Control (MAC) Sublayer Functions", INFOCOM'97. • R. O. Baldwin, N. Davis, and S. F. Midkiff, "A Real-time Medium Access Control Protocol for Ad Hoc Wireless Local Area Networks", ACM MC2R, Vol. 3, No. 2, 1999, pp. 20-27.
Handover latency reduction: • H. Kim, S. Park, C. Park, J. Kim, and S. Ko, “Selective Channel Scanning for Fast Handoff in Wireless LAN using Neighbor Graph”, ITC-CSCC 2004, July 2004. • S. Shin, A. S. Rawat, H. Schulzrinne, "Reducing MAC Layer HandoffLatency in IEEE 802.11 Wireless LANs", ACM MobiWac'04, Oct, 2004. • C.C. Tseng, K.H. Chi, M.D. Hsieh, and H.H. Chang, “Location-based fast handoff for 802.11 networks”, IEEE Communications letters, vol. 9, issue 4, pp. 304- 306, April 2005.
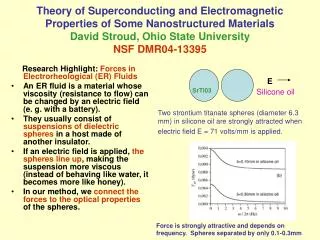
Research Highlight: DCF Performance Analysis • Ref: G. Bianchi, “Performance Analysis of the IEEE 802.11 Distributed Coordination Function”, IEEE J-SAC, 2000. • Assuming saturation situation (stations always have packets to transmit), the work analyze the DCF performance. • state of a station: (s(t), b(t)) • s(t): backoff stage (0, 1, …, m) of the station • CWmax = 2m Wmin • Let Wi = 2i W. • b(t): backoff counter value • p: colliding probability (a constant)
Some Important Transitions start backoff backoff 1 step failure, next stage successful trans. failure, max stage
Research Highlight: Unfair Access • Ref: K. Kanodia et al., “Ordered Packet Scheduling in Wireless Ad Hoc Networks: Mechanisms and Performance Analysis”, ACM MobileHoc 2002. • As there are multiple wireless links coexisting, some unfairness problem may arise. • Scenario 1: Asymmetric Information • throughputs ratio of A to B = 5% : 95% • reason: B knows more information than A does B A
B C A • Scenario 2: Perceived Collision • throughputs of A : B : C = 36% : 28% : 36% • reason: Due to spatial reuse, flow A and C can capture the channel simultaneously, thus causing flow B to reserve consecutive NAVs. • Proposed solution: “Distributed Wireless Ordering Protocol” • an ordered distributed packet scheduling for MAC • can be based on any reference scheduler, such as FIFI, Virtual Clock, Earliest Deadline First.
Research Highlight:Collision Avoidance and Resolution Multiple Access with Transmission Groups R. Garces and J. J. Garcia-Luna-Aceves INFOCOM’97
Abstract • a CARMA-NTG protocol for accessing wireless media • CARMA-NTG = Collision Avoidance and Resolution Multiple Access Protocol with Non-persisitent Trees and transmission Group • Based on transmission group • Once obtaining the medium, a station will have its right to keep on sending. • based on RTS/CTS messages
Concept of Cycles • Dynamically divide the channel into cycles of variable length. • Each cycle contains a contention period and a group-transmission period. • The group-transmission period is a train of packets sent by users already in the group. • New users contend to join transmission group by contending during the contention period. A, B, C Y, A, B, C Z, Y, A, B, C X, Z, Y, A, B, C media : contention period : group trans. period X Y Z
Each STA Needs to Keep Track of … • To send in the transmission period, each station must know the following environment parameters: • the number of members in the transmission group • its position within the group • the beginning of the each group-transmission period • the successful RTS/CTS exchange of new users in the previous contention period
Group-Transmission Period • A station transmits once the previous station’s packet is received. • The spacing is twice the propagation delay. • If this is not heard during this period, • assume that the previous station fails • its membership is removed from the group • the failed station has to contend to join the group later. B’s transmission exceeds propagation delay A B C A C A C B contend later
Contention Period • Contending based on RTS/CTS exchange. • The contention period terminates once the first station successfully join the group. • Each station runs the NTG scheme (non-persistent tree and transmission group) • Each station keeps the following variables: • a unique ID • LowID and HiID: to denote the current contention window in the current contention period • contention window: the allowable ID’s that can contend • an ID not within this range can not contend • a stack: the future potential contention windows
NTG Scheme • Initially, LowID=1 and HiID=(max. ID in the system) • On RTS conflict, all stations divide (LowID, HiID) into • (LowID, (LowID+HiID)/2) • ((LowID+HiID)/2 + 1, HiID) // i.e., binary split • PUSH the first part into STACK • Contend if its ID is within the latter part. • If no RTS is heard after channel delay, POP the stack and repeat recursively. • ONLY stations in the RTS state can persist in trying. • new stations: backoff and wait until the next period • already-in-group stations: not until they leave the group
Contention Example • A system with 4 stations: n00, n01, n10, n11. • n00 and n01 are contending. (a) (c) (b) (d) n01 RTS n00 RTS n11 idle n10 idle after idle after 2nd collision after n01 success before 1st collision after 1st collision (a) (b) (c) (d) (00, 01) (00, 00) allowed interval (00, 11) (10, 11) (00, 01) (01, 01) (00, 11) n01 RTS n00 RTS n01 RTS packets
Short Summary • propose the concept of group transmission • Only one RTS/CTS exchange is used for transmitting a train of packets • better fairness than IEEE 802.11 • NTG (non-persistent tree group) keeps the contention cost low. • Performance: • on high load, similar to TDMA • on low load, better than TDMA by getting rid of empty slots
Research Highlight:Polling Issue in IEEE 802.11 “Investigation of the IEEE 802.11 Medium Access Control (MAC) Sublayer Functions”, B. P. Crow, J. G. Kim, & P. Sakai, INFOCOM’97.
Problem Statement • In the PCF function of IEEE 802.11, it is NOT specified how to poll STAs. • Problem: how to do voice communication using PCF? • Assuming that all voice packets have the same priority. • Voice stream characteristic: • ON-and-OFF process • ON = talking; • OFF = listening low probability talk silent low probability
A “Round Robin” Approach • AP keeps track of the list of STAs to be polled. • When CFP begins, the AP polls the STAs sequentially. • If the AP has an MPDU to send, the poll and MPDU are combined in one frame to be sent. • O/w, a sole CF-Poll is sent. • When CFP ends, the AP keeps track of the location where the polling stops. • Then resume at the same place in the next CFP.
(cont.) • Within a CFP_Repetition_Interval, if an STA sends no payload in k polls, the STA is dropped from the polling list. • k is an tunable parameter • In the next CFP, the STA will be added back to the list again. • Basic Idea: to avoid useless polling.
Simulation results: • Smaller k gives better data throughput (Fig. 14). • k = 1~5 does not affect the voice delay (Fig. 15).
Short Summary • An interesting polling mechanism based on specific applications. • Future directions: how to support other types of media.
A Real-Time Medium Access Control Protocol for Ad Hoc Wireless Local Area Networks Main Idea: “send your next backoff value” ACM Mobile Computing and Communication Review, 1999, Vol. 3, No. 2, pp. 20-27.
Review of IEEE 802.11 • The CW (contention window) is initially CWmin, and is doubled after each failure, until CWmax is reached. • BV (backoff value) randomly in [0..CW-1]. • The BV is decreased after each idle slot.
Drawback of IEEE 802.11 • Can not meet the requirements of real-time communication. • When a packet has missed its deadline, the packet will still be buffered and sent. • Thus, this causes more contention, collisions, ... • more packets may miss their deadlines. • There are 4 rules (next few pages).
Rule 1:Enhanced Collision Avoidance • Announcing the next BV: • When a packet is transmitted, the next BV to be used is placed in a field of the packet. • Stations who hear this packet will avoid selecting this BV as their next backoff timer. • BV is a random number in [0..CW-1].
Details: • Prior to transmitting a packet, a station will select its next BV from the range of [0..CW-1], excluding those BV’s already chosen by other stations. • A station will indicate in its data packet the next BV value to be used. • A station should keep a table of BV values used by other stations. • After an idle slot, a station should decrease its own BV, as well as others’ BVs in its table.
Example: • A: 3 1 8 • B: 1 6 ... • C: 5 2 (collides with B’s, changed to 3) B(6) A(1) A(8) C(3) B(...) C(...) 0 1 2 3 4 5 6 7 …
Rule 2:Transmission Control • A station must send when its BV value has expired. • If the packet experiences transmission failure, it will be reexamined to see if its deadline has been missed. • Note: another backoff still has to be taken.
Rule 3:Contention Window Size • CW is set to 8N, where N is the estimated number of “real-time” stations. • N: can be estimated by counting the number of unique addresses for a period of time. • [alternative] N: a function of current channel load. • “8” is chosen by instinct. • Note: CW is thus not doubled after a transmission failure • (compared the original IEEE 802.11 of doubling each time).
Rule 4: Collision of BV • Due to mobility, transmission error, and collisions, a station may receive a packet indicating a BV equal to its own BV. • The station must select another BV value; otherwise, collision will occur. • To avoid the station being unduly penalized, the new BV should be selected from [0..CBV-1]. • CBV = its current BV. • I.e., the station is given higher priority. • If all values in [0..CBV-1] are chosen, then we double it (i.e., [0..2*CBV-1]).
Collision Ratio • RT-MAC is quite stable in collision prob. with respect to the number of stations.
Short Summary • A new RT-MAC protocol. • broadcasting the next BV value • BV depends on the current number of stations • Results: • The network behavior is quite stable in terms of mean delay, missed deadline ratio, and collision ratio. • The mean delay is quite independent of the number of stations.
How to reduce handover time? • Channel scanning in 802.11 is very time-consuming if all channels need to be scanned. • If scanning one channel takes 30 ms, the toally 300-400 ms is needed.
Research Highlight:Fast Channel Scanning by Neighbor Graph • Ref: H. Kim, S. Park, C. Park, J. Kim, and S. Ko, “Selective Channel Scanning for Fast Handoff in Wireless LAN using Neighbor Graph”, ITC-CSCC 2004, July 2004. • Method: • A concept called neighbor graph (NG) is proposed. From the NG provided by an external server, a MH only needs to scan the channels that are used by its current AP’s neighbors. About 10 ms are needed to scan a specific neighbor.
Research Highlight:Fast Channel Scanning by Caching • Ref: S. Shin, A. S. Rawat, H. Schulzrinne, "Reducing MAC Layer HandoffLatency in IEEE 802.11 Wireless LANs", ACM MobiWac'04, Oct, 2004. • Method: • MH maintains a cache which contains a list of APs adjacent to its current AP. • The cached data was established from its previous scanning. • Only the two APs with the best RSSI were cached. • During handoff, the cached APs are searched first. If this fails, scanning is still inevitable.
Research Highlight:Fast Channel Scanning by Location Information • Ref: C.C. Tseng, K.H. Chi, M.D. Hsieh, and H.H. Chang, “Location-based fast handoff for 802.11 networks”, IEEE Communications letters, vol. 9, issue 4, pp. 304- 306, April 2005. • Method: • MH can predict its movement path and select the potential AP. • A location server is needed to provide information of APs. • So a MH can re-associate with its new AP directly without going through the probe procedure. • However, this scheme relies on a precise localization method.
Other Readings • Medium Access Control • R. Garces and J.J. Garcia-Luna-Aceves, “Floor Acquisition Multiple Access with Collision Resolution,” Proc. ACM/IEEE MobiCom 96, Rye, New York, November 11-12, 1996. • Z. Tang and J.J. Garcia-Luna-Aceves, “Hop-Reservation Multiple Access (HRMA) for Ad-Hoc Networks,” Proc. IEEE INFOCOM '99, New York, New York, March 21--25, 1999. • V. Bharghavan, A. Demers, S. Shenker and Lixia Zhang, “MACAW: A Media Access Protocol for Wireless LAN's,” Proceedings of SIGCOMM 94, pp.212-225. • P. Karn, “MACA - A New Channel Access Method for Packet Radio,” ARRL/CRRL Amateur Radio 9th Computer Networking Conference, April 1990, pp.134-140. • Romit Roy Choudhury, Xue Yang, Ram Ramanathan, and Nitin Vaidya, “Using Directional Antennas for Medium Access Control in Ad Hoc Networks,” ACM International Conference on Mobile Computing and Networking (MobiCom), September 2002.