WP6: Static Analysis
This presentation by Flemming Nielson from the Technical University of Denmark discusses advancements in static analysis methods as applied to global computing systems. It covers the objectives of Work Package 6 (WP6) within the DEGAS project, focusing on language abstractions and the integration of qualitative and security analysis models. Key topics include the analysis of ambient calculi and π-calculi for access control, the development of the LySa tool for network security, and comparisons with competing approaches. The session also highlights new techniques for validating security protocols and addresses usability and exploitation perspectives of static analysis tools.

WP6: Static Analysis
E N D
Presentation Transcript
Presented by Flemming Nielson Informatics and Mathematical Modelling Technical University of Denmark at the 3nd review of DEGAS in April 2005 WP6: Static Analysis
static analysis security features class diagrams sequence diagrams UML design activity diagrams stochastic features Markov model The DEGAS view: WP5, WP6 reflection fully automatic and hidden from the user extraction model in process calculus
Objectives of WP6 • Comparing and finding new language abstractions to design global applications (D9 month 12) • Enhancing understanding and applicability of static analysis for global computing systems (D11 month 24, D14 month 33) • New models and techniques for integrated qualitative and security analysis statically • Proof-of-concepts implementations to validate the above treatment (D19 month 24).
Language Abstractions Within DEGAS we have considered analysis of • ambient calculi (for access control) • π-calculi (for access control and performance) • LySa (network security and performance) An overview of language abstractions are in D9: Basic Static Mechanisms of Process Algebras for Global Applications
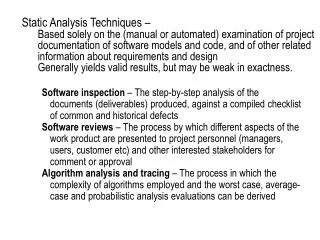
Static analysis (over-approximation) Actual behaviour Model checking / Theorem Proving (under-approximation) Basics of Static Analysis Characterising the behaviour:
Enhancing Static Analysis Network security • LySa and its static analysis Access control • π-calculus and Enhanced Operational Semantics Discussed in • D11 Models and Techniques for Static Analysis • D14 Final Report on Static Analysis
Analysis of LySa Over-approximation Attacker + Hardest attacker Static analysis Protocol Actual behaviour
Prototype: the LySatool Constraint generation Constraint solving LySa Constraints Solution Annotated with authentication properties Includes violations of authentication properties In Alternation Free Least Fixed-point logic • Details are in D19 Static Analysers • The LySatool in integrated in Choreographer • The LySatool is available on the internet: http://www.imm.dtu.dk/cs_LySa/lysatool
LySa Durring the Thrid Year • Developed a technique for tracking replay attacks • Implemented analysis of infinite scenarios • Improved efficiency of the LySatool to cater for industrial size protocols • Improved usability (input/output capabilities of the LySatool) • Discovered unknow security issues in • Classical security protocols (Beller-Chang-Yacobi ’93, Bauer-Bereson-Feiertag ’83) • Modern protocol standards (OASIS) • Case studies (D26)
Enhanced Static Analysis • Corrado, Pierpaolo, or Chiara: Please provide a slide (or two) with information about your contribution in D14
Integrating Security and Performance Analysis Design and analysis process Supported by performance analysis using: • PEPA – for timing attacks (facilitated by Choreographer) • EOS for protocol performance / effort spent on attacks Protocol in LySa Static security analysis OK Performance analysis Redesign protocol Not OK
Self-evaluation of WP6 Positioning with respect to state of the art • S1: Strong indicator for discovery of a new class of flaw in a protocol published in the literature • W1: Weak indicator for application to key exchange protocol for DEGAS case study Comparison with competing approaches • S2: Strong indicator for clarifying the fundamentally different behaviours of model checking and static analysis as regards protocol validation • W2: Weak indicator for termination properties of our analysis approach • W2: Weak indicator for allowing to use model checking to validate the flaws reported by static analysis.
Self-evaluation of WP6 Usability and explotation perspectives • S3: Strong indicator for hardening the design of the analysis tool so that also educated users outside of the research group (mainly MSc-students) are able to use the analysis tool. • W4: Weak indicator on the ability to analyse the OASIS protocol for Single Sign On. • W5: good progress towards weak indicator based on the UML to LySa extractor • S6: Strong indicator for the ability to teach the analysis method to advanced MSc-students and PhD-students that subsequently can use it for projects.