Mobility
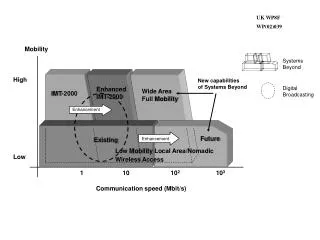
Mobility. Mobility Defined. Mobility is the main reason for wireless networks Mobility means the end-user device is capable of moving location in the networked environment


Mobility
E N D
Presentation Transcript
Mobility Defined • Mobility is the main reason for wireless networks • Mobility means the end-user device is capable of moving location in the networked environment • Roaming occurs when a wireless client moves association from one AP and re-associates to another, typically because its MOBILE! • Mobility presents new challenges: • Need to scale the architecture to support client roaming—roaming can occur intra-controller and inter-controller • Need to support client roaming that is seamless (fast) and preserves security
Scaling the Architecture with Mobility Groups • Mobility Group allows controllers to peer with each-other to support seamless roaming across controller boundaries • APs learn the IPs of the other members of the mobility group after the LWAPP Join process • Seamless Roaming across: • Rel 4.2 : 24 controllers , 3600 Aps • Rel 5.0 : 48 Controllers, 7200 APs • Rel 5.1 : 72 Controllers, 10,800 Aps • Mobility messages exchanged between controllers • Data tunneled between controllers in EtherIP (RFC 3378)
Roaming Requirements • Roaming must be fast… Latency can be introduced by: • Client channel scanning and AP selection algorithms • Re-authentication of client device and re-keying • Refreshing of IP address • Roaming must maintain security • Open auth, static WEP—Session continues on new AP • WPA/WPAv2 Personal—New session key for encryption derived via standard handshakes • 802.1x, 802.11i, WPA/WPAv2 Enterprise—Client must be re-authenticated and new session key derived for encryption
Fast Secure Roaming • Client channel scanning and AP selection algorithms—Improvedvia CCX features • Refreshing of IP address—Irrelevantincontroller-based architecture! • Re-authentication of client device and re-keying • Cisco Centralized Key Management (CCKM) • Proactive Key Caching (PKC)
Intra-Controller Roaming • Intra-Controller roam happens when an AP moves association between APs joined to the same controller • Client must be re-authenticated and new security session established • Controller updates client database entry with new AP and appropriate security context • No IP address refresh needed
Client must be re-authenticated and new security session established Client database entry moved to new controller No IP address refresh needed Layer-2 Roaming—Inter-Controller • L2 Inter-Controller roam happens when an AP moves association between APs joined to the different controllers but client traffic bridged onto the same subnet
Layer-3 Roaming—Inter-Controller • L3 Inter-Controller roam happens when an AP moves association between APs joined to the different controllers but client traffic bridged onto different subnet • Client must be re-authenticated and new security session established • Client database entry copied to new controller • Original controller tagged as the “Anchor” • New controller tagged as the “Foreign” • No IP address refresh needed • Asymmetric traffic path established
Layer-3 Roaming—Symmetric Mobility (4.1+) • Foreign controllers will send Layer 3 roaming client’s packet back to its anchor controller through EtherIP tunneling • Source IP address of the packet will be the foreign controller’s management IP address • Upstream routers that have Unicast Reverse Path Forwarding (uRPF) will forward on packets • Configurable option in software release 4.1 (Not the default)
Layer 3 MobilitySymmetric Tunneling • Default WLC tunnel behavior is asymmetrical • Must be explicitly enabled • Must be configured the same for all WLCs that are members of the mobility group
WLC 4.1 Feature - Anchor Wireless LAN Controller Failover Layer 3 Roaming • Client associates with Anchor wireless LAN controller and receives IP Address. • Client roams to new access point. • EtherIP tunnel to Anchor wireless LAN controller is established. • Foreign wireless LAN controller establishes heart beat with Anchor wireless LAN controller. • EtherIP tunnel to Anchor wireless LAN controller fails and Foreign wireless LAN controller notices missing heartbeat. • Foreign wireless LAN controller disassociates client. • Client is locally terminated. • Upon reconnection client obtains a new IP address. Foreign Wireless LAN Controller Heartbeat Fails Anchor Wireless LAN Controller EtherIP tunnel Cisco AironetLightweight Access Point Client Roams Client Device Client Device
Fast Secure Roaming for Secure VoiceProactive Key Caching (PKC) • Extension of Pairwise Master Key caching • Leverages client use of Master Key caching • Permits knowledge of Master Key before client roam to AP on new controller • Controller mobility group automatically exchangesthe key PMK Proactively Cached on New Controller PMK Derived Initial Authentication PMK Used In 4W Handshake Client Transmits Cached PMK upon New Association PMK Used in 4W Handshake Client Roam
Supporting Roaming—Design Best Practices and Caveats • Minimize inter-controller roaming in your designs • Design the network for <= 10msec RTT latency between controllers • Inter-controller layer-2 roaming is more efficient than layer-3 roaming • Layer-3 roaming—Consider the effects of things like uRPF and stateful security features in your designs • Use PKC or CCKM to speed up and secure roaming • Client roaming behavior—mileage varies by vendor, driver, supplicant. Look for CCXv4 feature-set to improve roaming behavior. (Remember it’s the client who makes the decision to roam.)